
API Security Buyer’s Guide
This Buyer’s Guide highlights the key capabilities necessary for a comprehensive API security platform.
{ "term_id": 161, "name": "Filip Verloy", "slug": "filip-verloy", "term_group": 0, "term_taxonomy_id": 161, "taxonomy": "wpx-authors", "description": "", "parent": 0, "count": 14, "filter": "raw" }
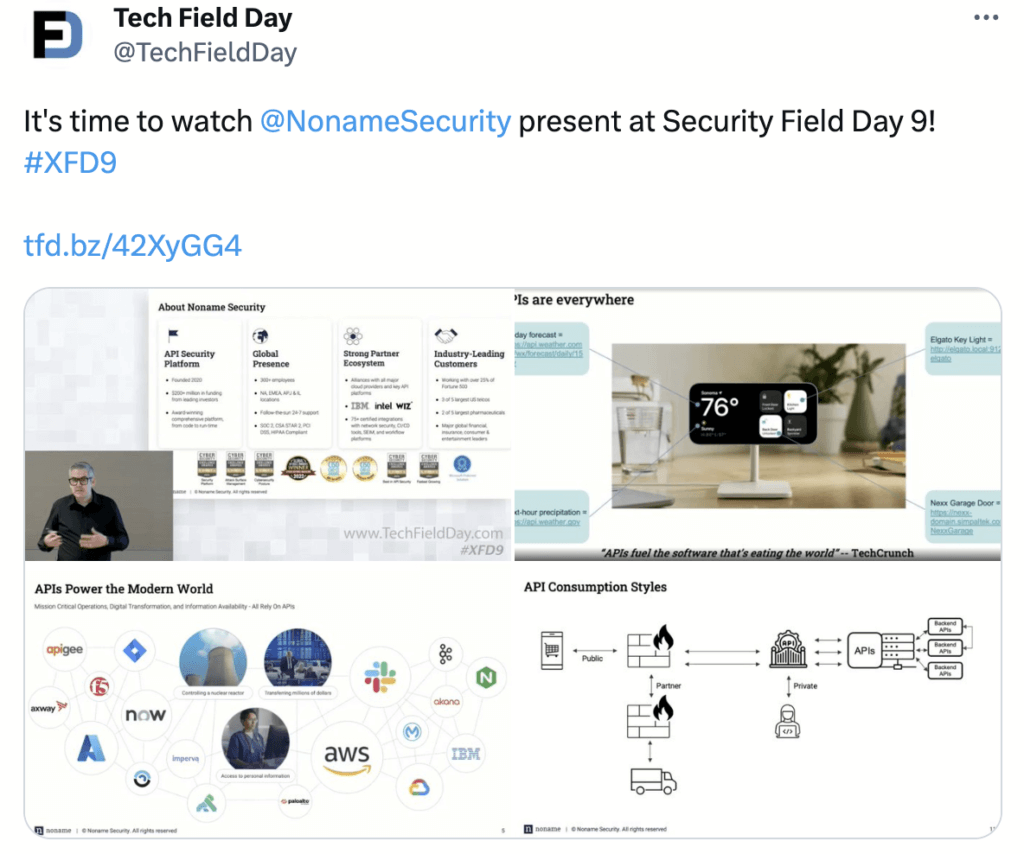
Noname Security had the distinct privilege to present at Security Field Day 9, held on June 28 in San Francisco. Security Field Day is part of the Tech Field Day series of events organized by Gestalt IT. It brings together industry luminaries to interact with the presenting vendors. These presentations are streamed live during the event and just got posted on their YouTube channel, hence this blog post.

We thoroughly enjoyed our inaugural attendance at the event and really appreciated the interactive discussions and feedback both during and after the event. The delegates for this 9th edition of the Security Field Day (abbreviated as XFD9, not SFD9, as the first event the Tech Field Day team put on was Storage Field Day, so the “S” was spoken for) were;
And Tom Hollingsworth (https://techfieldday.com/people/tom-hollingsworth/) as part of the organizing team. Some delegates could attend in person, and others remotely. Both sets provided valuable feedback, and we loved interacting with them. The delegates also relayed questions coming in via Twitter (https://twitter.com/search?q=%23XFD9&src=typed_query) from people attending the session live around the globe (PT timezone permitting, of course).
We started our series of 3 presentations with a high-level introduction of our company, Noname Security, the problem of API security, and how existing solutions have a real blind spot for this specific attack vector.
Session 2 focused on a live demo of the platform. As we understood, live demonstrations of the actual product are always much preferred over slides. We dedicated most of our time to this one.
Edgar Ortiz, Noname’s Director of Solution Architects, East, demonstrated our core platform consisting of Discovery, Posture Management, and Runtime Security.
Our 3rd and final session was about creating secure APIs using our Active Testing platform. Tomer Semo, Noname’s Active Testing Group Manager, talked about the challenges of testing APIs and where traditional security testing tools fall short. He then jumped into a demo overview of the solution.
Next to the live questions, the delegates also did some excellent write-ups on our session. Some of them I’ve posted below (I’ll update the blog if more come in).
“With a deep understanding of the escalating risks associated with API vulnerabilities, Noname Security has developed a comprehensive suite of solutions that address the shortcomings of traditional security measures.” – Source
“My takeaway from today’s briefing is that Noname’s product is a stunner — something you should consider adding now to the security product arsenal.”
Source
“Noname Security presented two essential services to facilitate API transitions seamlessly. Firstly, their monitoring solution tracks API calls, providing insights into usage patterns and ensuring the correct utilization of data types. While not a web application firewall (WAF), this solution can trigger actions in response to anomalous activity, alerting other systems when something is amiss. Secondly, Noname Security provides an API testing service that calls API functions and attempts to insert invalid data both based on what was learned by their monitoring and by using OWASP recommended methods. By incorporating this service into the CI/CD pipeline, developers receive prompt feedback in case of any unexpected behavior.” – Source
“Lots of applications have an API now. Many apps have those APIs on by default, with a default security posture. What can you do with that API? It depends, but for many apps, APIs are the primary interaction method. In that case, you can do EVERYTHING. Whatever the app is capable of, the API facilitates. That, to me, is the “hidden” aspect of APIs as an attack surface. Depending on an API’s capability, an attacker has potentially read-write access to all info the API provides.”
This was a great event, getting feedback from a deeply technical independent audience always makes for a great learning experience. We appreciated the candid feedback and were blown away by the positive comments.
If there is one organizational learning I can take away from this, it is that next time we need to implement some better time management. It is hard to guesstimate the appropriate mix of slide content vs the amount of questions you think you will get. We could have shared lots more cool stuff, but found it more appropriate to engage with the delegates for Q&A, but that is also good news, as we still have so much more things to share next time!
As the field of cyber security is really about working together inside a larger ecosystem we found branching out to the community at large a natural extension of our mission to secure the world’s modern application environments.