Platform Features
By Need
By Industry
Partner Program
Our Partners
Resource Center
{ "term_id": 294, "name": "Stas Neyman", "slug": "stas-neyman", "term_group": 0, "term_taxonomy_id": 294, "taxonomy": "wpx-authors", "description": "", "parent": 0, "count": 9, "filter": "raw" }
The Noname Security 3.24 release supports a connection status view for resources discovered through API Gateway and Load Balancer integrations, adds a preview of a new Traffic Audit capability, and enables configuration of the Noname Telemetry service within the Noname platform UI.
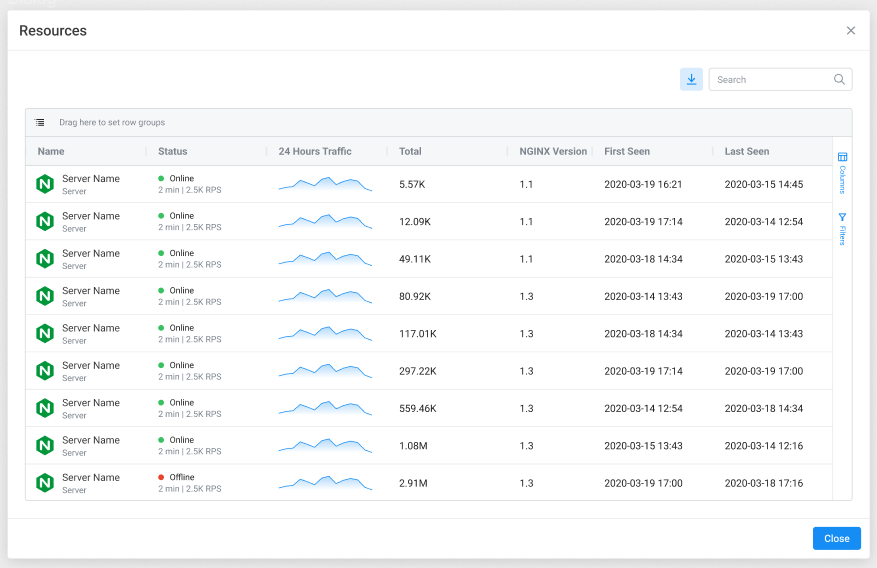
Noname Security platform can now support connection status view for resources discovered through NGINX, Mulesoft, Apigee, F5, and Kong integrations. Previously, resource connection status was available for cloud resources hosted on AWS and Azure. Now, you can capture the connection status and additional attributes for resources connected to the Noname Security platform through API Gateway and Load Balancer integrations. This lets you quickly determine which resources send traffic to your Noname platform and identify failed connections or disconnected resources.
For example, you can now see if a server discovered through your NGNIX integration is still online and double-check its NGINX version. You can also see details for applications connected to your Mulesoft instance, including traffic sent to the Noname platform over the last 24 hours, application versions, and environments in which apps are deployed. The attributes discovered by this feature are automatically populated in your Inventory view to make monitoring and troubleshooting your environment easier.
To learn more about this feature, please visit the Traffic Sources documentation.
Traffic Audit is a new capability of the Noname Security platform that allows you to record, visualize, and analyze API traffic in your environment. Once enabled, Traffic Audit records API data flows matching specific criteria across your application environments, including typical and anomalous API activity. This makes it easier for you to discover and manage the risk exposure of suspicious users and unusual API behaviors. Each Traffic Audit can be custom-tailored to your particular use case, allowing you to capture and retain traffic according to pre-determined filters and rules.
For example, you can create a Traffic Audit for all APIs captured by the Noname Security platform that contain personally identifiable information and originate outside your corporate IP range. The resulting information can be used to perform forensic analysis for specific attacks, investigate suspicious user behavior, or troubleshoot your API configurations.
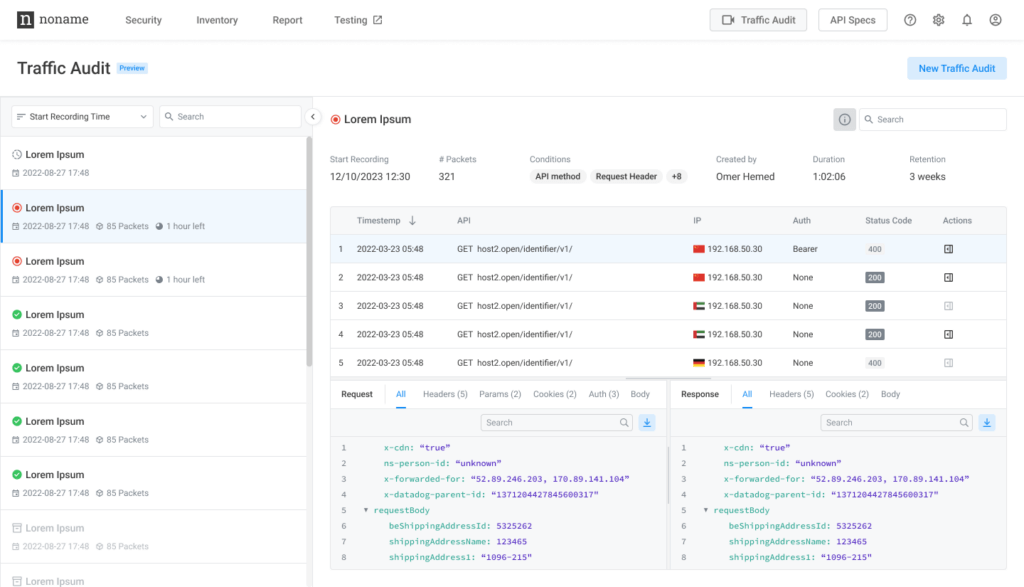
In addition, Traffic Audit includes granular search and filtering capabilities. This allows you to hone in on particular data flows, assess specific API behavior, and create incidents based on traffic patterns. For instance, after addressing a known API vulnerability, you can perform a highly targeted Traffic Audit to validate the resolution or identify additional APIs that need your attention.
The Traffic Audit feature is currently in Private Preview. Please contact your Noname Security account representative to learn more about enabling Traffic Audit capability in your environment.
With this release, we add the flexibility to granularly control the Noname Telemetry Service permissions directly within the Noname platform user interface. The Noname Telemetry service, an optional capability for both SaaS and on-premises Noname Security deployments, allows the Noname support team to monitor system health remotely.
When enabled, the Telemetry Service automatically and securely collects essential system information necessary for monitoring the health of your servers. It also generates support cases when system metrics exceed expected levels. This significantly reduces support resolution times and allows Noname to address reliability issues with your deployment proactively. The Support Settings page updated in this release now provides a transparent view into the current state of the Telemetry service configuration, enables you to opt in or out of all system monitoring services, and includes controls for turning extra support services on or off.
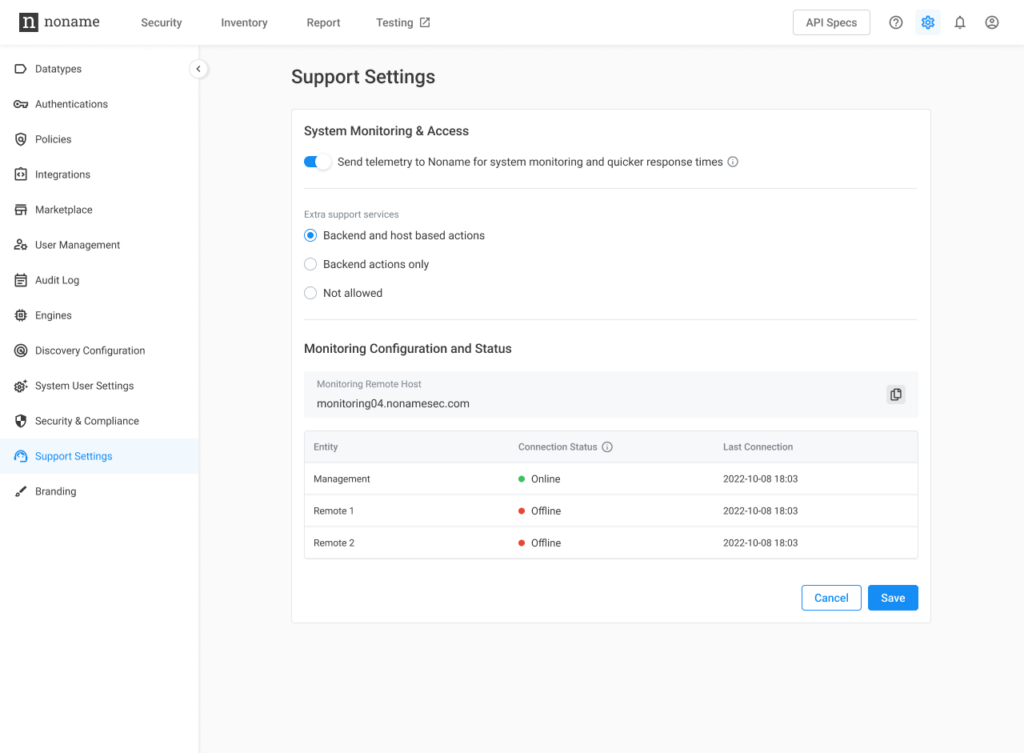
To learn more about the Noname Telemetry service, please visit the Noname Documentation site.
For additional information about the Noname Security 3.24 release, please review the release notes.