
Definitive Guide to API Discovery
Shadow and rogue APIs operating freely are putting your organization at risk.
{ "term_id": 162, "name": "Harold Bell", "slug": "harold-bell", "term_group": 0, "term_taxonomy_id": 162, "taxonomy": "wpx-authors", "description": "", "parent": 0, "count": 82, "filter": "raw" }
Key Takeaways
This blog highlights how Gartner’s new report, Everything You Should Do to Address API Security, is literally a 1:1 mapping to the Noname API Security Platform. Read this blog to discover just how well we align to the Gartner API security domains.
World-renowned analyst firm, Gartner, recently published a research piece entitled, Everything You Should Do to Address API Security, which is a compilation of all their latest research on the subject. More importantly, it maps out the key domains that you need to be aware of, and invest in, if you take your API security posture seriously.
With that said, I found it quite interesting how well aligned their API security domains are to the Noname API Security portfolio. The framework Gartner delivered is literally a 1:1 mapping to our platform. So you can imagine how excited I am to write this blog.
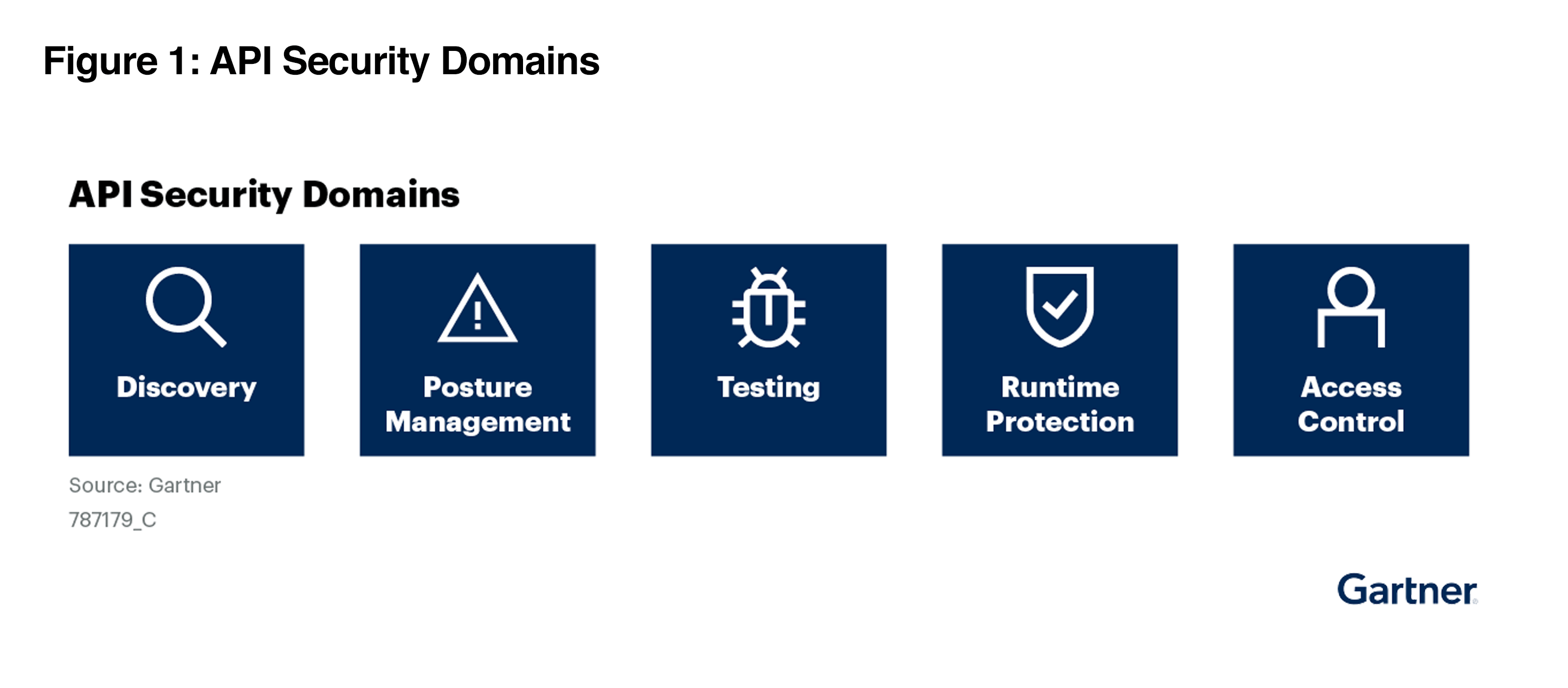
In the following paragraphs, I’m going to walk you through the 5 key API security domains Gartner introduced, what they mean, and ultimately how Noname Security provides a solution for each area.
As Gartner points out, “this is a good first step for almost any API security initiative.” Why? Well, Gartner predicts that 50% of enterprise APIs will be “unmanaged” by 2025, which means that observability will be limited at best. In case you’re new to the term, API discovery is the process of locating all the APIs within your organization – including legacy, dormant, and shadow APIs. By having this level of visibility, API discovery enables enterprises to maintain an accurate inventory of their APIs at all times.
Noname Security provides just the granular visibility required to find and fix your APIs, which includes validating unmanaged APIs. We help organizations identify just how many APIs they have, no matter the type – including HTTP, RESTful, GraphQL, SOAP, XML-RPC, JSON-RPC, and gRPC. We can also locate shadow domains and subdomains that were previously unknown, unmanaged, or forgotten. Which is critical considering that Gartner says, “unmanaged and unsecured APIs are easy targets for attacks, increasing vulnerability to security and privacy incidents.”
Now that you have an inventory of your APIs, Gartner states that “the second step would typically be to perform an assessment of the security of these APIs. This means identifying misconfigurations with the APIs.” In addition to misconfigurations, posture management allows you to uncover known vulnerabilities and compliance violations. It’s important to keep in mind that posture management is a tool for APIs in production. We’ll tackle security controls for pre-production APIs in the next section.
As far as posture management goes, Noname looks at the widest possible set of sources to detect vulnerabilities, including log files, replays of historical traffic, and configuration files. The tool also can detect some of the vulnerabilities in the OWASP API Security Top 10. Or let’s say you might have a WAF service as part of your public cloud infrastructure, but if you have a routing issue, you might not send all API traffic through it. We can detect these things with our Posture Management module.
To top things off, we provide insights into the types of data that traverse your APIs – things like credit card information, health records, social security numbers, etc. The purpose here is to help organizations maintain better control over customers’ personally identifiable information (PII), and remain compliant with regulations such as GDPR, HIPAA, CCPA, etc.
Though many developers stop at API functionality testing or use traditional application security tests for APIs, the honest truth is that these approaches won’t suffice. According to Gartner, “traditional AST tools — SAST, DAST and interactive AST (IAST) — were not originally designed to test for vulnerabilities associated with typical attacks against APIs.”
They go on to say that, “to identify the optimal approach to API testing, they are looking to a mix of traditional tools (such as static AST [SAST] and dynamic AST [DAST]) and emerging solutions focused specifically on the requirements of APIs.” When you think about the latter part of this quote, they are talking about purpose-built API security testing.
But it’s not just about testing alone. When you test your APIs is also of great importance. Gartner adds that “as your maturity increases, this testing should be increasingly embedded in the development life cycle and vulnerabilities should be remediated as they are uncovered, before they are pushed into production.” This is where Noname Security shines.
Noname Active Testing provides a suite of over 150 API-focused security tests that SecOps can run on-demand or as part of a CI/CD pipeline to ensure that APIs aren’t implemented with security vulnerabilities in them. While fuzzing can certainly be part of the toolkit, our API specific approach leaves no API untested. With our platform, developers can now release more secure code at scale, build API security into the design, and make fixes early in the development process.
Runtime protection refers to the process of safeguarding APIs while they’re operating and managing requests. The goal is to detect and avoid malicious API calls. Ultimately, when you think about blocking API attacks, your runtime protection tool is the means of doing so. However, it’s important to understand that blocking runtime API threats requires an ability to protect data by leveraging more context. Gartner also advises that organizations consider “adding behavioral anomaly detection using API protection products.”
As if we wrote the guidelines ourselves, Noname conducts real-time traffic analysis and provides contextual insights into potential security gaps. We use automated AI and ML-based anomaly detection to identify data leakage, data tampering, data policy violations, suspicious behavior, and API security attacks.
It’s also important to note that our Runtime Protection detects the remaining vulnerabilities in the OWASP API Security Top 10 that weren’t picked up by our Posture Management module . This isn’t a sign of weakness of either module, rather each has a different set of responsibilities, therefore detecting different vulnerabilities. And to streamline remediation, our Runtime Protection tool integrates with your existing ITSM, SIEM, and SOAR systems so issues can be automatically assigned to the appropriate teams as they are identified.
A new addition to the Gartner list of API protection capabilities, “access control is best addressed at design time. It addresses issues such as how to authenticate to the API, and how to authorize access to the client.” Gartner also states that “some misconfigurations and vulnerabilities can still be remediated after testing the API, but may require structural changes that lead to modifications to the infrastructure and the API itself.”
As our customers can attest, Noname Security is well positioned in both instances. During the design and development phase, our Active Testing solution can help organizations address authentication and authorization gaps before production. And once APIs are deployed, our Posture Management module can uncover any vulnerabilities related to user access, while our Runtime Protection module can remediate any exploits that were the result of compromised access.
As you can see, the Noname API Security Platform clearly checks all the boxes when it comes to lining up against the Gartner best practices. To get a more in-depth understanding of what to look for in your evaluation of an API security platform, I strongly recommend downloading our ebook, the API Security Buyers Guide. It provides a detailed look at all of the capabilities discussed above.